Prof. Powershell
Certificate Certainty
A map of your computer's certificate store can be navigated by way of PowerShell.
- By Jeffery Hicks
- 09/11/2012
One of the more useful PowerShell providers is the Certificate provider. I don't think it gets as much attention as it should. This provider maps your computer's certificate store as a navigable "file " system. In this structure you can see what certificates are installed, where they came from and when they expire.
Getting to this "drive" is no different than changing to any other drive:
PS C:\> cd cert:
The PSDrive name is 'cert' but when you want to navigate to it, you need to include the colon. But now we have a file-like system we can navigate like any other drive, although the structure may be a little different (see Fig. 1).
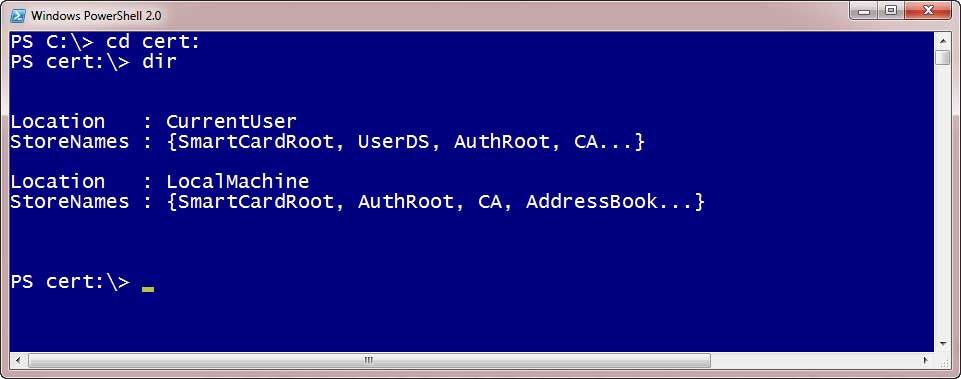 |
Figure 1. Changing to the CERT: PSDrive. (Click image to view larger version.) |
Sometimes it is hard to tell what is a container or "sub-folder" but hopefully the Location property gives it away. This is where tab completion comes in handy. Start typing Localmachine and press tab to auto-complete followed by Enter. Not sure what to do next? Type DIR. You should see something like Fig. 2.
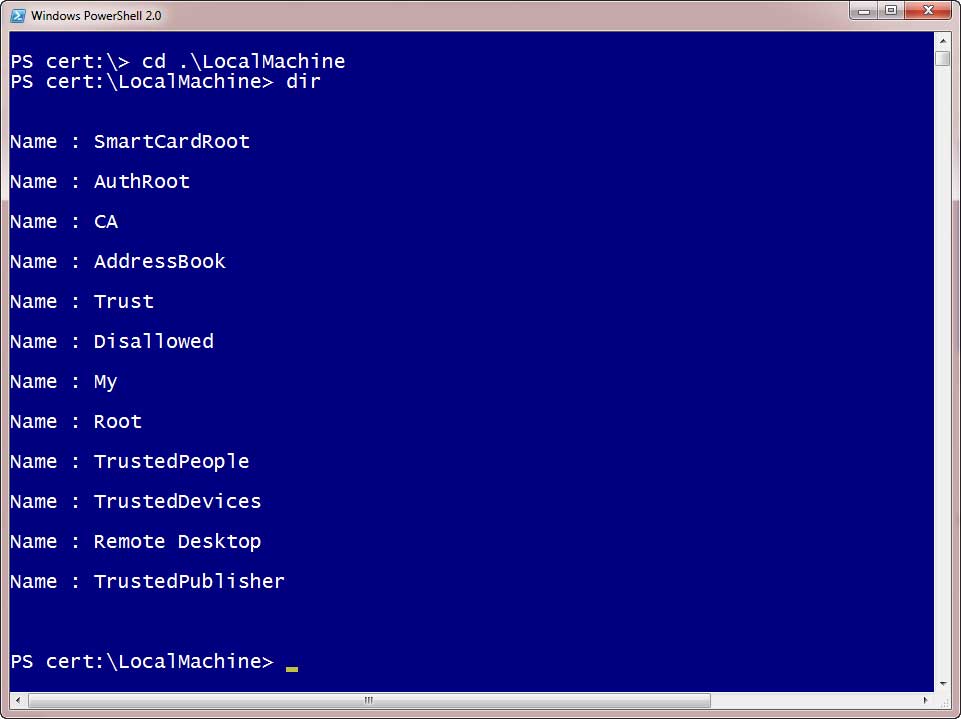 |
Figure 2. Changing Directories. (Click image to view larger version.) |
Each of the names you see is another container. Let's see what is in the Root container:
PS cert:\LocalMachine> cd root
PS cert:\LocalMachine\root> dir
What you see in Fig. 3 are certificate objects.
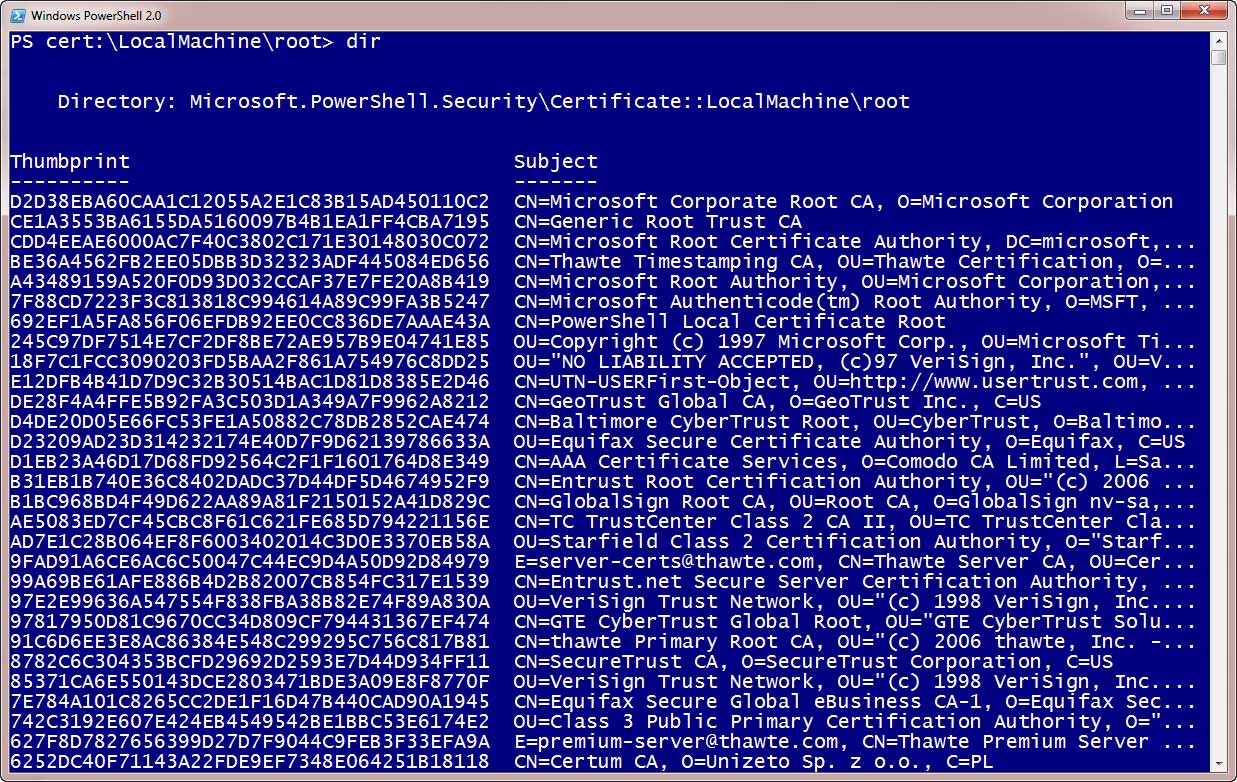 |
Figure 3. Certificate Objects. (Click image to view larger version.) |
As with most default displays in PowerShell, there is more to the object than what you see on the screen. We could use Get-Member to learn more about these objects:
PS cert:\LocalMachine\root> dir | get-member
But I find it easier to look at one with a command like this:
PS cert:\LocalMachine\root> dir | select -last 1 | select *
Fig. 4 depicts the result.
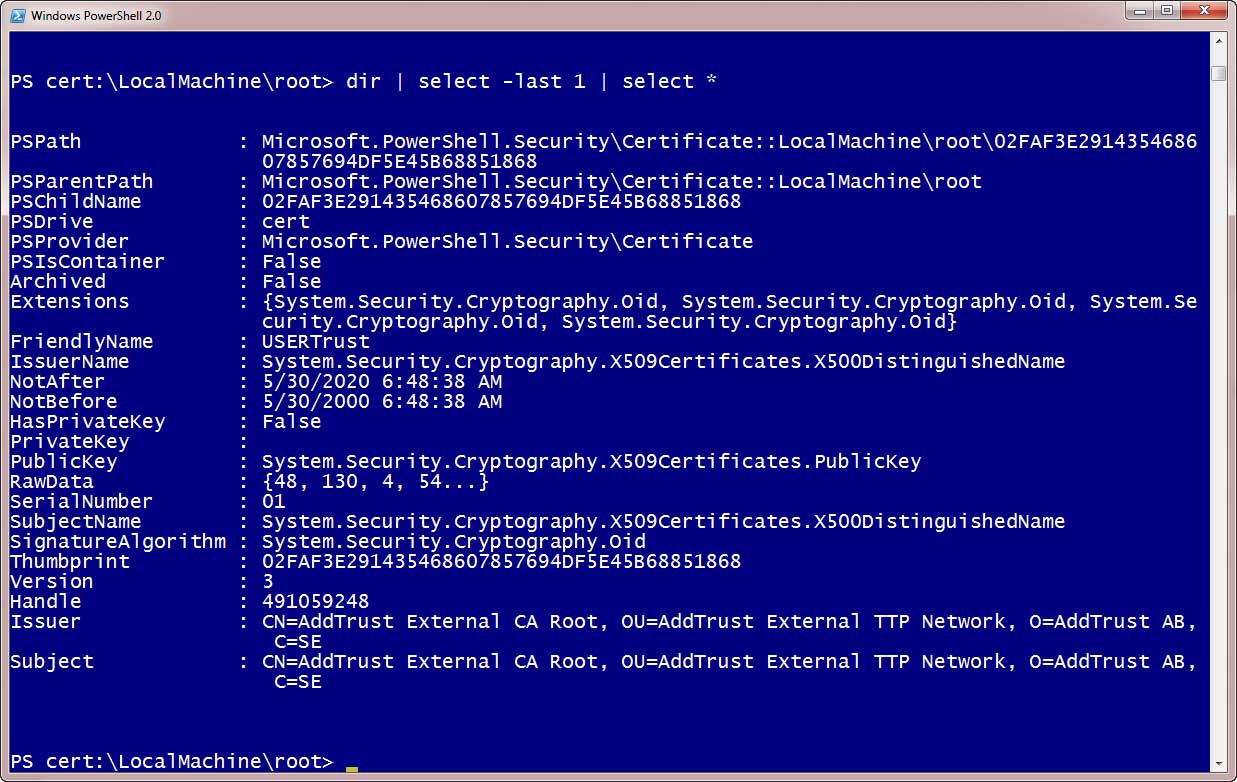 |
Figure 4. A Certificate Object. (Click image to view larger version.) |
By the way, a neat little trick here is to use the object to launch the certificate manager GUI tool:
PS cert:\LocalMachine\Root> dir | select -last 1 | invoke-item
This won't open the specific certificate but launches the GUI.
Anyway, now that I know some property names I can use PowerShell to display more useful information such as where these certificates came from:
PS cert:\LocalMachine\root> dir | sort Subject | select Subject
Or more important, which ones have expired?
PS cert:\LocalMachine\root> dir | where {$_.NotAfter -lt (Get-Date)} | Select NotAfter,Subject
As you see in Fig. 5 I have several that are no longer valid.
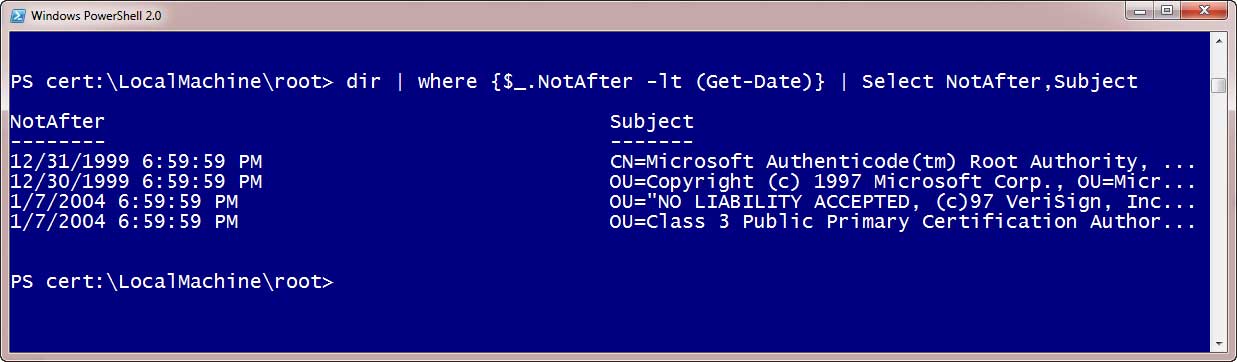 |
Figure 5. Expired Certificates. (Click image to view larger version.) |
What if I decide to delete them? Normally I would first run a command like this:
PS cert:\LocalMachine\root> dir | where {$_.NotAfter -lt (Get-Date)} | del -whatif
This should work but I get an error that the provider doesn't support this operation, even though Get-PSProvider shows it allows SupportsShouldProcess. In fact it seems the provider won't even delete anything. Whether by design or bug it is unfortunate. Fortunately, PowerShell 3 has a command that will work for our purposes.
Finally, you can only access the CERT: drive locally. But once you get a command that works locally, then you can use Invoke-Command to run it on remote computers.
You can learn more about the Certificate provider by running: help certificate.
About the Author
Jeffery Hicks is an IT veteran with over 25 years of experience, much of it spent as an IT infrastructure consultant specializing in Microsoft server technologies with an emphasis in automation and efficiency. He is a multi-year recipient of the Microsoft MVP Award in Windows PowerShell. He works today as an independent author, trainer and consultant. Jeff has written for numerous online sites and print publications, is a contributing editor at Petri.com, and a frequent speaker at technology conferences and user groups.