Prof. Powershell
My Favorite PowerShell 4 Features (Part 2)
Prof. PowerShell is back again to share another batch of his favorite tweaks in the latest version of Powershell.
- By Jeffery Hicks
- 12/17/2013
See Also:
In the previous lesson I highlighted some of my favorite features in PowerShell 4.0. Here are a few more. These are items that I think you might want to use immediately in your PowerShell management tasks.
Get-FileHash
Years ago I wrote a function to derive a file hash based on the MD5, SHA1 or SHA256 algorithms. This came in handy when verifying a file copy. Now PowerShell 4.0 has a Get-FileHash cmdlet that does the same thing. Give the cmdlet the path to a file and the hashing algorithm and you'll get a checksum. Valid algorithms are SHA1, SHA256, SHA384, SHA512, MACTripleDES, MD5 and RIPEMD160. The default is SHA256.
PS C:\> get-filehash .\unattend.xml | Select Hash
Hash
----
A281E0CB7C2A7858DED2CEBBDD383B58604C2C4E1CB8E04A11773C466E4797FA
The result is an object with the algorithm and hash. You could get the file hash of an entire directory and save it.
PS C:\> dir scripts -file | get-filehash -Algorithm MD5 | export-csv c:\work\scripthash.csv
Or verify that a file was copied correctly.
PS C:\> $before = Get-FileHash C:\scripts\CHI-CORE01.mof -Algorithm MD5
PS C:\> $after = copy C:\scripts\CHI-CORE01.mof -Destination \\chi-fp02\SalesData -PassThru | get-filehash -Algorithm MD5
PS C:\> compare-object $before $after -Property hash
As long as the file copies OK, Compare-Object won't return anything.
Get Process Owner
Another enhancement that I think IT Pros will like is the ability to display process owner with Get-Process.
PS C:\> get-process -IncludeUserName
You can see the result here:
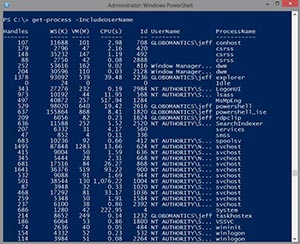 [Click on image for larger view.] Figure 1.
[Click on image for larger view.] Figure 1.
Having access to this information offers up some interesting possibilities. How about displaying all non-system owned processes?
PS C:\> get-process -IncludeUserName | where {$_.username -match "globomantics"} |group Username
Count Name Group
----- ---- -----
6 GLOBOMANTICS\jeff {System.Diagnostics.Process (conhost), Syste...
1 GLOBOMANTICS\rgbiv {System.Diagnostics.Process (notepad)}
The caveat is that only works locally. You can't get user names with Get-Process using –Computername. However, you can use PowerShell remoting.
PS C:\> invoke-command {get-process -IncludeUserName | where Username } -comp chi-hvr2 | out-gridview -title "CHI-HVR2 Processes"
I ran this from a Windows 8.1 system to a Windows Server 2012 R2 server.
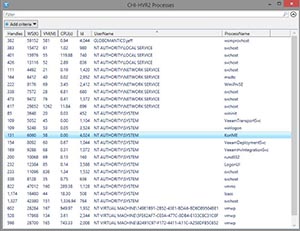 [Click on image for larger view.] Figure 2.
[Click on image for larger view.] Figure 2.
But because the command is running on the remote server, you can use remoting from any version of PowerShell. Here's a command from a PowerShell 2.0 session querying processes on Windows 8.1.
PS C:\> invoke-command {get-process -includeusername | where {$_.username -match "globomantics"}} -comp chi-win81.globomantics.local -Credential globomantics\administrator
However, as you can see in the screen shot, PowerShell 2.0 doesn't know by default about the new property.
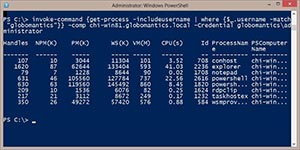 [Click on image for larger view.] Figure 3.
[Click on image for larger view.] Figure 3.
But all that means is that you need to take an extra step to display it.
PS C:\> invoke-command {get-process -includeusername | where {$_.username –match "globomantics"}} -comp chi-win81.globomantics.local -Credential globomantics\administrator | Format-table ID,ProcessName,WS,Username –auto
Here's the result:
 [Click on image for larger view.] Figure 4.
[Click on image for larger view.] Figure 4.
Sure, it isn't as elegant but it works.
PowerShell 4.0 has much to offer an IT Pro so I hope you'll get your hands on it and give it a go. Oh, and be sure to reread help even for cmdlets you think you know just in case there is some little enhancement that might be just what you need.
About the Author
Jeffery Hicks is an IT veteran with over 25 years of experience, much of it spent as an IT infrastructure consultant specializing in Microsoft server technologies with an emphasis in automation and efficiency. He is a multi-year recipient of the Microsoft MVP Award in Windows PowerShell. He works today as an independent author, trainer and consultant. Jeff has written for numerous online sites and print publications, is a contributing editor at Petri.com, and a frequent speaker at technology conferences and user groups.