PowerShell Pipeline
Exploring the Active Directory Forest and Domain
Use the Active Directory Module to run available cmdlets and automate many of your daily tasks.
Back in the day, we would be using ADSI to connect to our Active Directory forest/domain to gather information about a variety of things. Today I will completely ignore ADSI and focus solely on the Active Directory module to show how to leverage the available cmdlets to not only explore your environment, but also to perform various tasks that you may encounter in your day-to-day activities.
Note: I will be running PowerShell V5 on Windows 10 for today's article. Some commands may not be available in older versions.
One of the many jobs of a system administrator is working with Active Directory and making sure that they know what is going on in their environment. A great way to better understand how things work is by exploring the environment and taking note of what your forest and domains are and how they are configured. Fortunately for us, we have the ActiveDirectory module available to assist in viewing everything.
If you are missing the ActiveDirectory module, then you will need to ensure that you have it available. In the case of Windows 10, you can download the Remote Server Administation Tools (RSAT) and then run the installer to make the module available to you.
Now we can verify that we are ready to get started on our adventure with Active Directory!
 [Click on image for larger view.] Figure 1. Checking to see if the module is available.
[Click on image for larger view.] Figure 1. Checking to see if the module is available.
For those of you running this on a server, the process is actually easier than this! All you have to do is run the following command to install the module and then you too can get started as well.
Install-WindowsFeature -Name RSAT-AD-PowerShell
Checking out the Forest
The first thing that I am going to do is take a look at the Active Directory forest and see how it is configured. To do that, I will use the Get-ADForest cmdlet and see what it returns. First thing to do though is to check out the help just to see what is available. This is useful whenever you are working with cmdlets that you are not sure about or just need a refresher on what is available.
Get-Help Get-ADForest
 [Click on image for larger view.] Figure 2. Looking at the help for Get-ADForest.
[Click on image for larger view.] Figure 2. Looking at the help for Get-ADForest.
I don't really need to do anything special other than just calling the cmdlet.
Get-ADForest
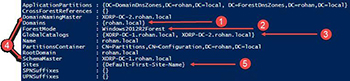 [Click on image for larger view.] Figure 3. Viewing the forest information.
[Click on image for larger view.] Figure 3. Viewing the forest information.
From here we can see that my forest, rohan.local has the following:
- One Domain in the forest
- The forest functional level is Windows2012R2
- I have two Global Catalogs
- My Forest level FSMO roles (Domain Naming Master and Schema Master) are split between two Domain Controllers
- I have one site
Now that we know what the forest looks like, let's take a look at the domain using Get-ADDomain.
Get-ADDomain
 [Click on image for larger view.] Figure 4. Viewing the information of a domain.
[Click on image for larger view.] Figure 4. Viewing the information of a domain.
Here we can see the following in the domain:
- The default location where computers that are joined to the domain are automatically placed
- The location of the Domain Controllers when promoted in a domain
- The current domain functional level
- The domain FSMO roles, which are spread between two domain controllers
- The default location of new users created in the domain
So, we have information about the forest and from the domain. What is next on the list?
If you answered the Domain Controller, then you would be correct! We can view the domain controller information by using the Get-ADDomainController cmdlet.
Get-ADDomainController
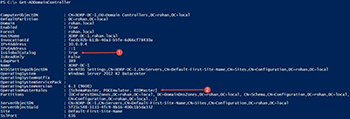 [Click on image for larger view.] Figure 5. Viewing a domain controller.
[Click on image for larger view.] Figure 5. Viewing a domain controller.
- Shows that this domain controller is a global catalog
- Shows the FSMO roles which are hosted on this domain controller
This cmdlet has some other nice parameters such as –AvoidSelf (does not include itself if run on a domain controller) along with –Discover (shows another discoverable domain controller).
We can also view the trust of the forest using the Get-ADTrust cmdlet and take note of any possible trust configurations.
Get-ADTrust –Filter *
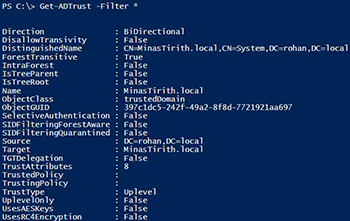 [Click on image for larger view.] Figure 6. Taking a look at the trust of a forest.
[Click on image for larger view.] Figure 6. Taking a look at the trust of a forest.
Continuing on with the replication exploration, I will use Get-ADReplicationSite to view the Active Directory Site replication.
Get –ADReplicationSite
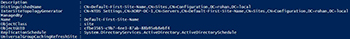 [Click on image for larger view.] Figure 7. AD replication site information.
[Click on image for larger view.] Figure 7. AD replication site information.
In this case, I only have one site in my environment and can find out more about this site using Get-ADSiteReplicationLink.
Get-ADReplicationSiteLink –Filter *
 [Click on image for larger view.] Figure 8. Looking a the site links.
[Click on image for larger view.] Figure 8. Looking a the site links.
So with that, we have gone through our forest and domain and learned more about the environment using just a small set of PowerShell cmdlets available from the Active Directory module. But don't stop exploring now that this article has finished! Keep charging forward and before you know, you will have some nice documentation about your Active Directory environment in no time!
About the Author
Boe Prox is a Microsoft MVP in Windows PowerShell and a Senior Windows System Administrator. He has worked in the IT field since 2003, and he supports a variety of different platforms. He is a contributing author in PowerShell Deep Dives with chapters about WSUS and TCP communication. He is a moderator on the Hey, Scripting Guy! forum, and he has been a judge for the Scripting Games. He has presented talks on the topics of WSUS and PowerShell as well as runspaces to PowerShell user groups. He is an Honorary Scripting Guy, and he has submitted a number of posts as a to Microsoft's Hey, Scripting Guy! He also has a number of open source projects available on Codeplex and GitHub. His personal blog is at http://learn-powershell.net.